Unlock Your Career Potential
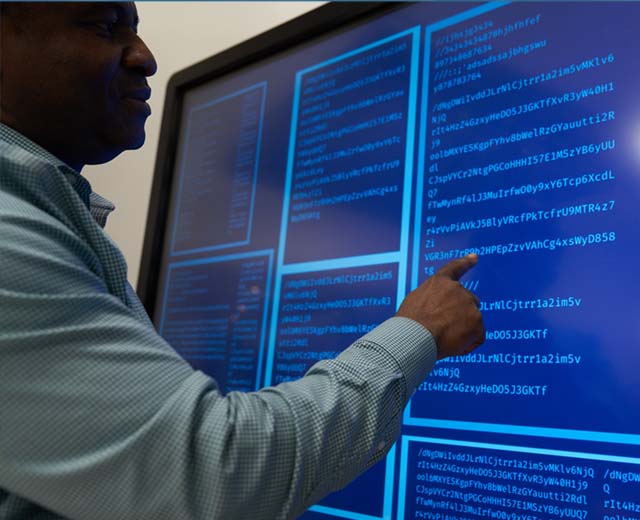
This program is designed to help you prepare for cybersecurity management careers in many professional contexts. The skills you gain in this program translate to a number of industries, including healthcare, finance, homeland security, information security, and many more. UMGC courses are taught by experienced faculty and address skills and competencies that are highly valued by today’s employers.




/blog-umgc-cybersecurity-pen-test-linklist-shutterstock-2373338757.jpg)
/blog-banner-linklist-cybersecurity-program_shutterstock_2499480585.jpg)
/blog-banner-linklist-drazek-winners_mock-drazek-crystal-award.jpg)